Cybercrime, broadly defined as unlawful behaviour involving the use of computers – either as a tool for committing a crime (such as cyber stalking) or as the target of a crime (such as identity theft) – comes in a number of shapes and disguises and this “reasonably short” (i.e. quite long) PowerPoint Presentation can be used to introduce some of the main types.
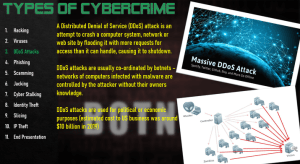
These include, in no particular order:

As you may have noticed these types all involve, to greater or lesser extents, access to a networked system of computers – hence the idea of cybercrime: “crime that takes place in cyberspace”: pretty much a defining feature of contemporary computer crime.
The Presentation introduces students to some different varieties of cybercrimes by:
The list is indicative rather than exhaustive and you’ll find there’s a lot of overlap between the entries. It’s probably best to think of them as overlapping categories (“hacking”, for example, may involve the distribution of a virus or malware whose objective is identity theft) rather than discrete types.
The obvious reason for this is to reinforce the idea that there’s nothing particularly special or different about cybercrimes: they generally (but not always) have an underlying economic motive involving the same or very similar common-or-garden motives underlying “real world” crimes such as theft, fraud or harassment. The main difference, of course, is that the crime is carried-out using a computer.
This is very much just a “ballpark figure” to suggest the potential economic costs of different types of cybercrimes. It’s difficult to reliably calculate global costs, partly because losses may be hidden – individuals don’t know they have been victimised, corporations don’t advertise their victimisation – partly because different countries have different ways of calculating and reporting costs and partly because of the aforementioned overlap between different types of cybercrime.
Finally, I haven’t included any specific examples of each type of cybercrime for one of two reasons (please delete as inapplicable):
1. The Presentation is designed for use as a discussion-prompt or as the basis for further exploration. This means you can include your own examples of each type as and how you want.
2. Putting the Presentation together took a lot longer than I’d intended and I got bored didn’t get around to including examples (although this is something I might decide to do as part of any future update).
Share This Post
Related
Discover more from ShortCutstv
Subscribe to get the latest posts sent to your email.

